Google recently removed 106 more extensions from its Chrome Web Store after they were found illegally collecting sensitive user data as part of a “massive global surveillance campaign” targeting oil and gas, finance, and healthcare sectors.
Awake Security, which disclosed the findings late last week, said the malicious browser add-ons were tied back to a single internet domain registrar, GalComm.
However, it’s not immediately clear who is behind the spyware effort.
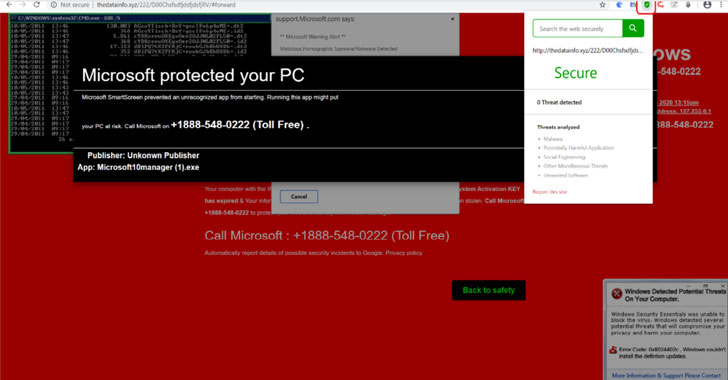
“This campaign and the Chrome extensions involved performed operations such as taking screenshots of the victim device, loading malware, reading the clipboard, and actively harvesting tokens and user input,” Awake Security said.
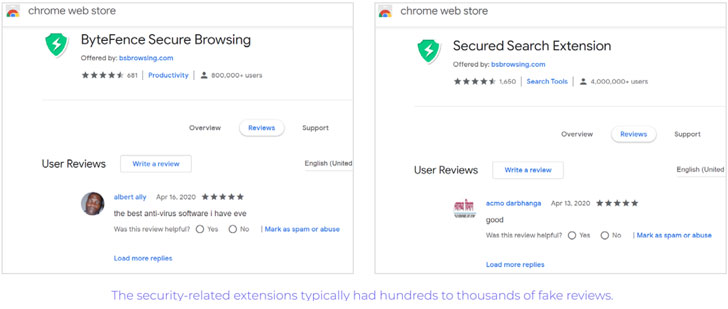
The extensions in question posed as utilities offering capabilities to convert files from one format to the other, among other tools for secure browsing, while relying on thousands of fake reviews to trick unsuspecting users into installing them.
Furthermore, the actors behind the operation leveraged evasion techniques to avoid flagging the domains as malicious by anti-malware solutions, thereby allowing the surveillance campaign to go undetected.
In total, the extensions were downloaded nearly 33 million times over the course of three months before Awake Security reached out to Google in May.
The search giant, in response to the disclosures, has deactivated the problematic browser extensions. The full list of offending extension IDs can be accessed here.
Telemetry data has revealed that some of these extensions were active on the networks of “financial services, oil and gas, media and entertainment, healthcare and pharmaceuticals, retail, high-tech, higher education, and government organizations,” although there’s no evidence that they were actually used to collect sensitive data.
“Galcomm is not involved, and not in complicity with any malicious activity whatsoever,” the Israel-based registrar’s owner Moshe Fogel told Reuters, which broke the development.
Deceptive extensions on the Chrome Web Store have continued to be a problem, what with bad actors exploiting it for malvertising and other data-stealing campaigns.
Earlier this February, Google removed 500 malware-ridden extensions after they were caught serving adware and sending users’ browsing activity to attacker-controlled servers. Then in April, the company yanked another set of 49 extensions that masqueraded as cryptocurrency wallets to steal Keystore information.
It’s recommended that users review extension permissions by visiting “chrome://extensions” on the Chrome browser, consider uninstalling those that are rarely used, or switch to other software alternatives that don’t require invasive access to browser activity.


0 Commentaires